#046: Perfect Forward Secrecy
Right now, Alice and Bob have a very secure way of encrypting communication using symmetric encryption algorithms. Alice and Bob can also share the required secret key using public key cryptography. But this method still left them with a problem: If an attacker, like Eve, simply stored all the encrypted communication between Alice and Bob, and later either manages to break public key cryptography, or manages to get ahold of either Alice’s or Bob’s private key, then she could still decrypt everything that was sent.
(And again, I’ll gloss over a lot of both the mathematical and technical details, but hopefully the links provided will satisfy your curiosity, should you want to know more)
To prevent this, Alice and Bob need a way to share a secret, without ever transmitting that secret in any way. At first glance, this sounds almost impossible. How can you share something without sharing it?
Thanks to Whitfield Diffie and Martin Hellmann, there is a way to do just that. They outlined an algorithm on how Alice and Bob can create a shared secret over an insecure channel, even if Eve is listening in the whole time.
Like RSA, Diffie-Hellmann relies on modular arithmetic, but the algorithm itself can be quite easily demonstrated using colors.
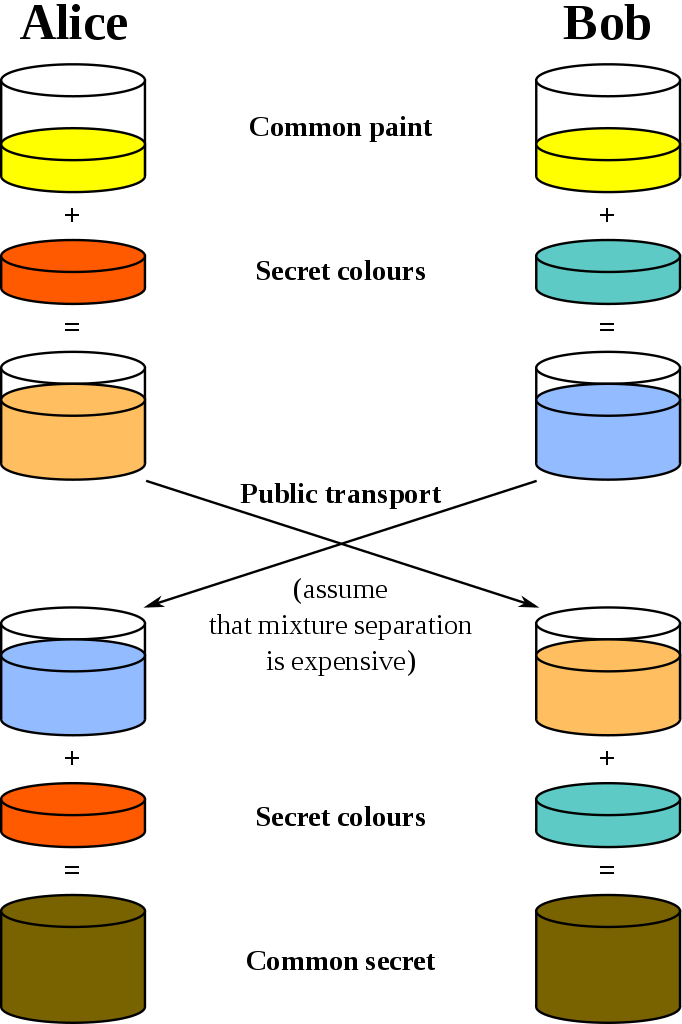
Both Alice and Bob start out by deciding on a common color (like yellow), and also each separately decide on a secret color (a light red for Alice, and teal for Bob). Then, they each mix their secret color with the common color (resulting in a light orange for Alice, and a light blue for Bob), and send the results to each other. Eve, who was listening in the whole time, knows about the common color yellow, and the mixtures Alice and Bob sent to each other, but has no idea about their secret colors.
Now Alice has Bob’s mixture, and vice versa. Here’s the trick: They each now mix in their own secret color again. Alice adds her own secret to the mixture of Bob’s secret color with the public color, and Bob does the same with his secret color with Alice’s mixture. Now both Alice and Bob have arrived at exactly the same color (brown with a light greenish tint) without ever sharing it in the first place.
This example relies on the assumption that separating colors is hard, which isn’t really true, but it is true if, like RSA, you use modular arithmetic.
Now, while this is a way to exchange a secret value with someone else, Diffie-Hellmann doesn’t provide any guarantees about who you’re exchanging that value with. If Eve wanted to, she could execute a so-called Man in the Middle attack, intercepting both Alice’s and Bob’s communication. For Alice, she impersonates Bob, and to Bob, she appears to be Alice. This would allow her to set up a shared color with Alice, and a shared color with Bob, and thus enable her to decrypt all the traffic between Alice and Bob.
So in practice, Diffie-Hellmann is used together with a public-key algorithm like RSA, in order to use the secure signing capabilities to authenticate Alice and Bob to each other. This way, Alice knows she’s exchanging a secret with Bob and no one else, while at the same time generating a key in such a way that Eve couldn’t reconstruct it later on even if she recorded all the communication between Alice and Bob.
In fact, we now have almost all the building blocks we need to securely communicate with anyone on the internet. The only problem now is to know who we can trust.
This is where your operating system vendor comes in. They preload your operating system with a set of trusted providers and their public keys in the form of certificates. In turn, if Alice wants to set up her web server with secure communications, she can get a certificate from one of those trusted vendors. When Bob visits her website, his browser will use RSA to authenticate Alice’s server certificate. And since it was signed by a trusted provider as defined by his operating system vendor, Bob can then use Diffie-Hellmann to generate a key for this session, which is then used to actually encrypt all the traffic between Bob’s and Alice’s computers. Afterwards, both delete the key, since they can generate a new one next time anyway.
And thus, even if Eve listens in and stores all the encrypted traffic, she has no choice but to brute-force the encryption keys in order to get at the contents. Neither Alice nor Bob have a private key Eve could steal to decrypt their traffic.
And this is what, on a very high, general level, happens every time you open a website using HTTPS.
Other interesting links from around the web:
📖 Weekly Longread 📚
Digital messages mimic the speed of real conversation, but often what people like best is the ability to put them off. : How It Became Normal to Ignore Texts and Emails

 (
(